What Is ELMS?
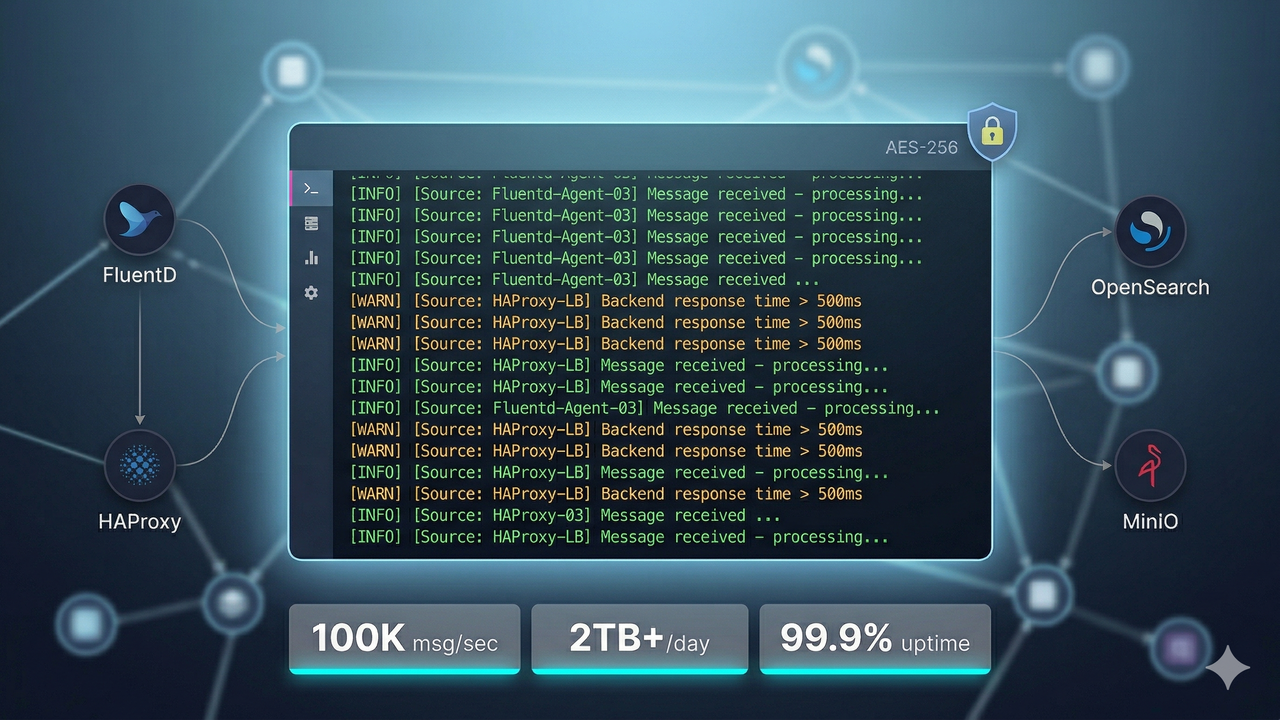
CloudControl's Enterprise Log Management System (ELMS) is a production-grade, compliance-ready centralized log management platform built on Graylog, OpenSearch, and MinIO — augmented with lowtouch.ai's private Agentic AI for autonomous detection, correlation, and remediation. ELMS is purpose-built for enterprises that need to handle massive log volumes, meet strict regulatory requirements, and reduce the operational overhead of manual log analysis.
At a glance:
- 50% Faster Log Retrieval across distributed systems
- 30% Faster Incident Response through real-time intelligent alerting
- 99.9%+ Uptime with high-availability clustering and HAProxy load balancing
- 180 Days Compliant Log Retention meeting RBI, ISO 27001, GDPR, SOC 2, CERT-In, and DGCA SMS requirements
- 100,000 Messages/Second sustained ingestion throughput
- 70% Reduction in Manual Tasks via lowtouch.ai Agentic AI automation
Core Capabilities
1. Massive Scale, Zero Data Loss
ELMS is engineered to ingest and process over 2TB of logs per day at sustained throughput of 100,000 messages per second — without data loss, even during peak traffic spikes. Built on a horizontally scalable Graylog cluster with HAProxy load balancing and OpenSearch as the search and analytics backbone, the platform handles:
- Multi-source log ingestion from applications, infrastructure, network devices, and API gateways
- Automatic routing of log streams via FluentD or Logstash to the appropriate Graylog input
- Fault-tolerant message queuing to prevent ingestion gaps during node failures
2. Tiered Storage Architecture
Not all logs need the same access speed or retention period. ELMS implements a two-tier storage model:
- Hot Tier (OpenSearch): 7-day rolling retention with full-text search and millisecond query response — ideal for active incident investigation
- Archive Tier (MinIO): 180-day compliant long-term storage with compressed, encrypted log bundles — satisfies RBI, CERT-In, GDPR, and ISO 27001 audit retention requirements
Automatic lifecycle policies move logs from hot to archive without manual intervention, and archive retrieval is available on demand for compliance audits.
3. Security-First Data Design
Logs frequently contain sensitive data — personally identifiable information (PII), session tokens, payment data, and credentials. ELMS enforces security at every layer of the pipeline:
- AES-256 encryption for data at rest in both OpenSearch and MinIO
- TLS 1.2+ encryption for all data in transit across every pipeline component
- PII masking at ingestion time — sensitive fields (card numbers, national IDs, email addresses) are masked or hashed before they reach storage, preventing unauthorized access even for platform administrators
- Immutable audit trails — log entries cannot be modified or deleted outside the defined retention policy window
4. Enterprise RBAC and Identity Integration
ELMS connects directly to your enterprise identity infrastructure:
- Active Directory (AD) and LDAP integration for single sign-on (SSO) and group-based access control
- Role-Based Access Control (RBAC) with granular stream and dashboard permissions — a developer can see application logs without accessing security or audit streams
- Team-scoped dashboards — each business unit or operations team sees only the log data they are authorized to access
- Session logging and access auditing — every login, search query, and dashboard view is recorded for compliance review
5. Real-Time Intelligence and Alerting
Static log dashboards are not enough for modern enterprise operations. ELMS delivers proactive, intelligent alerting:
- Prometheus metrics exporter for Graylog cluster health, ingestion lag, and indexing performance
- Grafana dashboards with pre-built panels for log volume, error rates, top talkers, and compliance metrics
- Alertmanager integration for routing critical alerts to PagerDuty, Opsgenie, Slack, or email
- Threshold and anomaly-based alerts — trigger on absolute counts, percentage spikes, or sudden drops in expected log volume
- Cross-stream correlation rules — detect multi-step attack patterns or cascading failures across different system log sources
6. Advanced Log Correlation Engine
Graylog's correlation capabilities, combined with OpenSearch's full-text analytics, enable ELMS to connect events across systems:
- Correlate authentication failures in Active Directory with network anomalies detected in firewall logs
- Link application errors to upstream infrastructure events for faster root cause analysis (RCA)
- Build event sequences (pipelines) that detect known attack patterns such as brute-force login attempts followed by privilege escalation
- Export enriched correlation alerts to your SIEM platform for enterprise security operations integration
Architecture Overview
ELMS follows a clean, three-stage pipeline:
Applications, Infrastructure, Network Devices, Databases
↓
FluentD / Logstash (Collection and Forwarding Agents)
↓
HAProxy (Load Balancing and High Availability)
↓
Graylog Cluster (Ingestion, Processing, Routing, Alerting)
↓
OpenSearch (Search, Analytics, 7-Day Hot Tier)
↓
MinIO Archive (180-Day Compliant Long-Term Storage)
This architecture ensures no single point of failure from the collection agent through to long-term archival. Each layer is independently scalable — you can add Graylog nodes to increase ingestion capacity, expand OpenSearch capacity for faster search, or grow MinIO storage as retention requirements change.
Universal Compatibility
ELMS integrates with every component of a modern enterprise technology stack:
| Category | Supported Sources |
|---|---|
| Operating Systems | RHEL, CentOS, Ubuntu, Windows Server |
| Container Platforms | Kubernetes (all distributions), Docker Swarm |
| API Gateways | Kong, NGINX, AWS API Gateway, Azure API Management |
| Databases | PostgreSQL, MySQL, MS SQL Server, Oracle, MongoDB |
| Network Devices | Cisco, Palo Alto, Fortinet, Juniper (Syslog/SNMP) |
| SIEM Platforms | Splunk, IBM QRadar, Microsoft Sentinel (log forwarding) |
| Applications | Any application that outputs to stdout, file, or syslog |
Compliance Coverage
ELMS is designed to meet the audit and compliance requirements of regulated industries:
| Framework | Coverage |
|---|---|
| RBI (Reserve Bank of India) | 180-day log retention, audit trail integrity, access control documentation |
| ISO 27001 | Information security event logging, access log review, incident management evidence |
| SOC 2 Type II | Availability, confidentiality, and security criteria for log infrastructure |
| GDPR | PII masking at ingestion, right-to-erasure workflow support, data residency controls |
| CERT-In (India) | Mandatory log retention for 180 days as per CERT-In 2022 directives |
| DGCA SMS | Safety Management System log evidence for aviation-regulated organizations |
ELMS vs. Alternatives: Honest Comparison
| Capability | CloudControl ELMS | Legacy ELK Stack | Splunk / Datadog / QRadar |
|---|---|---|---|
| Scale | 2TB+/day, 100K msg/sec | Degrades above 500GB/day | High, but cost-prohibitive |
| Compliance (CERT-In / RBI) | Built-in 180-day archive | Manual configuration required | Add-on modules at extra cost |
| PII Masking | At ingestion (native) | Post-ingestion (brittle) | Available, complex to configure |
| RBAC | AD/LDAP native | Plugin-dependent | Native, but expensive licensing |
| Agentic AI | lowtouch.ai (private, on-prem) | Not available | Cloud-only AI add-ons |
| Total Cost | Fixed managed service | High infra + ops overhead | Per-GB/per-host pricing adds up fast |
| Deployment Model | On-prem, private cloud, hybrid | On-prem or cloud (DIY) | SaaS or on-prem (Splunk) |
| Vendor Lock-in | None (open-source core) | Low | High (Splunk) / Medium (Datadog) |
lowtouch.ai Agentic AI Layer
ELMS is augmented with lowtouch.ai's private Agentic AI platform, which adds autonomous intelligence on top of the log management foundation:
SRE Agent Integration
The SRE Agent connects directly to Graylog and OpenSearch to:
- Detect anomalies in log volume, error rate, and latency patterns before they become incidents
- Perform automated root cause analysis (RCA) by correlating log events with infrastructure metrics from Prometheus and Grafana
- Trigger remediation workflows — restarting services, rolling back deployments, scaling pods — without human intervention
- Generate incident summaries in natural language and create Jira/ServiceNow tickets automatically
Compliance Agent
The Compliance Agent continuously monitors your log infrastructure for compliance drift:
- Verifies that log retention policies are enforced and archive jobs complete successfully
- Scans for PII masking gaps introduced by new application log formats
- Generates audit-ready compliance reports on demand for ISO 27001, RBI, and CERT-In audits
- Alerts on access control anomalies such as users accessing streams outside their authorized scope
AI/ML Anomaly Detection
Beyond rule-based alerting, the AI layer applies machine learning to:
- Learn baseline log patterns per service, time-of-day, and day-of-week
- Flag deviations from baseline without requiring manual threshold tuning
- Reduce alert fatigue by suppressing known-noisy alerts during maintenance windows
- Surface high-signal, low-noise incident candidates for SRE review
Case Study: Large Indian Financial Institution
Challenge: A large Indian financial institution with 2TB+ of daily log volume was running a legacy ELK stack that had become operationally unsustainable. Key problems:
- Elasticsearch degraded under peak ingest load, causing log gaps during high-traffic periods
- No RBAC implementation — all IT staff had unrestricted access to all log streams including audit and payment logs
- No PII masking — customer account numbers, national ID fields, and transaction references were stored in plaintext
- No long-term archive — logs were deleted after 30 days, failing RBI's 180-day retention mandate
- Manual alert management — SRE team spent 4–6 hours per day triaging Kibana dashboards
What CloudControl Delivered:
- Deployed Graylog cluster + HAProxy for high-availability ingestion at 2TB+/day with zero data loss
- Implemented OpenSearch as the hot-tier search backend with automated index lifecycle management
- Configured MinIO-based 180-day compliant archive with AES-256 encryption and immutable retention policies
- Deployed PII masking pipelines at ingestion — card numbers, Aadhaar fields, and email addresses masked before reaching storage
- Integrated AD/LDAP-based RBAC — 12 distinct access roles mapped to business units (application teams, network ops, security team, internal audit)
- Built Prometheus/Grafana monitoring stack with Alertmanager routing to PagerDuty for P1/P2 incidents
- Deployed lowtouch.ai SRE and Compliance Agents for autonomous anomaly detection and audit reporting
Outcomes:
- 50% faster log lookup — average query time dropped from 8 seconds to under 4 seconds across all teams
- 30% faster incident response — automated alerting and AI-assisted RCA reduced mean time to resolution (MTTR)
- 70% reduction in manual log management tasks — automated archival, masking, and compliance checks replaced daily manual processes
- 99.9%+ platform uptime — HA clustering with HAProxy eliminated single-node failure outages
- Full RBI compliance achieved — 180-day retention, audit trail integrity, and access control documentation passed the institution's internal audit within 6 weeks of go-live
Deployment Approach
CloudControl deploys ELMS in four structured phases to minimize business disruption:
| Phase | Duration | Activities |
|---|---|---|
| Phase 1: Foundation | 5 days | Infrastructure provisioning, Graylog cluster setup, HAProxy configuration, initial connectivity testing |
| Phase 2: Integration | 11 days | FluentD/Logstash agent deployment across all source systems, stream routing configuration, RBAC setup, AD/LDAP integration |
| Phase 3: Compliance | 19 days | MinIO archive configuration, lifecycle policies, PII masking pipelines, encryption validation, retention policy testing |
| Phase 4: Intelligence | 33 days | Prometheus/Grafana stack, Alertmanager routing, lowtouch.ai agent deployment, anomaly detection baseline training, compliance dashboard build |
| Phase 5: Handover | 1 day | Documentation, runbook handover, team training, go-live sign-off |
Get Started
CloudControl's ELMS is available as a fully managed service, including ongoing SRE support, compliance reporting, and lowtouch.ai Agentic AI operations.
To discuss your log management requirements:
- Email: info@ecloudcontrol.com
- Website: www.ecloudcontrol.com
- USA: +1 800 248 0296
- India: +91 994 656 641