AWS Landing Zone
WHAT IS AWS LANDING ZONE?
Foundation for AWS migrations.
Are you planning for cloud migrations?
Cloud adoption is increasing rapidly across organizations. More and more workloads are being moved to cloud every day. It is essential that you need a good cloud migration strategy in place for successful migrations. Lack of effective strategies can lead to higher costs, longer migration cycles or even failure.
Before you deploy your applications on Amazon Web Services (AWS), you need to design and configure a base environment. Traditional methods of setting up a multi account environment in AWS take significant amount of time and effort. It involves setting up of configurations, security, VPC, logging and enabling a set of other AWS services and settings to reach the baseline requirements.
Landing Zone,
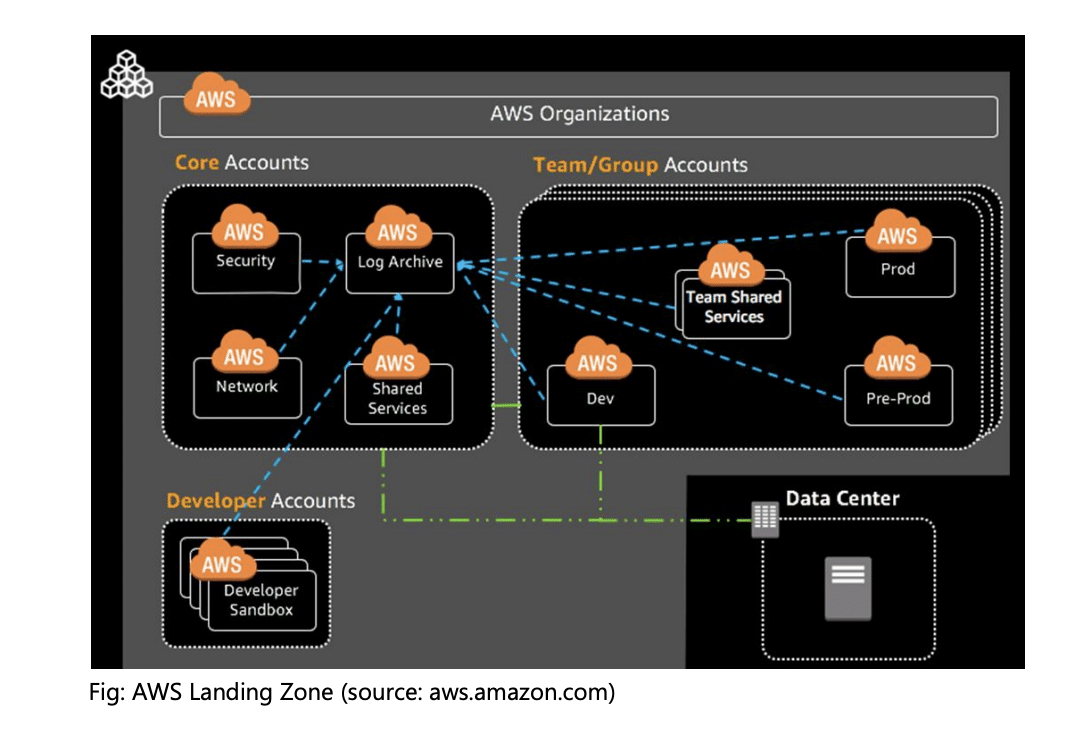
a new solution by AWS, which helps customers to easily setup secure, scalable, multiaccount environments based on best practices. It is an orchestration framework for your foundational AWS environment. It provides a baseline to get started with multi-account architecture, identity and access management, governance, data security, network design and logging. This solution saves time by automating the setup of an environment for running secure and scalable workloads, while implementing an initial security baseline through the creation of core accounts and resources.
Key Benefits
- Automation of AWS environment setup (IaC)
- Saves time, effort and cost
- Account vending machine
- Multi account management
- Creates baseline security
- Identity and access management
- Centralized logging
- Fully managed service
- AWS provided best practices, guardrails and compliance
- Effective governance and operational model
- Agility and business resiliency
BEST PRACTICES IN CREATING LANDING ZONE
Look at how successful businesses operate!
One can always develop custom methods and practices of working and find out which one is the best. But this approach is inefficient, costly, time consuming and failure prone. A far more effective approach would be to look at successful businesses, and find out and use industry’s best practices and standards. AWS recommends various Landing Zone best practices, including multi-account structure, security controls, self-service with guardrails, scalability, and extensibility from the initial landing zone environment, and automation with Infrastructure as Code (IaC).
- Organizations master account: It is the root account which provisions and manages member accounts at the organization level under AWS Organizations Services.
- Core accounts in an Organizational Unit: This provides essential functions that are common to all the accounts under the Organization, such as log archive, security management, and shared services like the directory service.
- Team/Group accounts in Organizational Units: Teams and groups are logically grouped under Teams. These are designated for individual business units at the granularity of team or group level. For example, a set of Team accounts may consist of the team’s shared services account, development account, pre-production account, and production account.
- Developer accounts: Enterprises should have separate “sandboxes” or developer accounts for individual’s learning and experimentation, as a best practice.
- Connectivity: is set up with default networking patterns among the accounts and with external data centres, which enable enterprises to have hybrid or multi cloud driven cloud adoption.
COMMON MISTAKES
Learn from mistakes and move on.
Some of the common mistakes and errors while using AWS Landing Zone are:
- Not using the right automation tools
- Lack of response to confirmation email messages
- Failed stack sets due to lack of enabling required STS regions
- New account provisioning fails due to invalid entries in provisioning form
- Failures to enrol an existing account due to Account Factory settings
- Unable to update Landing Zone due to closed or suspended accounts
- AWS Config errors
- Not enough permission errors
ROLE OF AUTOMATION
Choosing the right automation tool is work half done.
Automation aids in achieving efficiency through increased productivity, reliability, scalability, faster time to market, optimal use of resources, better quality, security and best practices. AWS Landing Zone solution automates landing zone deployment and configuration, which otherwise is a cumbersome task.
AWS has three options for creating your landing zone:
- A service-based landing zone using AWS Control Tower: This approach helps you to save time by automating the setup using best practices and guidelines of AWS Control Tower. Control tower uses other AWS services like Service Catalog and Organizations to provision accounts and manage access to accounts.
- A CloudFormation solution built using AWS Landing Zone: AWS CloudFormation can be used to automate the deployment of the AWS Landing Zone on the AWS Cloud. It uses pre-defined AWS CloudFormation templates, which can also be customized to your needs. AWS CloudFormation template enables AWS Organizations in an account, creates an Amazon S3 bucket and Landing Zone configuration zip file, an AWS CodePipeline for creating and updating the landing zone baseline. (AWS CodePipeline is a continuous integration and continuous delivery service for fast and reliable application and infrastructure updates). This solution leverages AWS CloudFormation StackSets, a collection of AWS resources that you can manage as a single unit, to enable you to create, update, or delete stacks across multiple accounts and AWS Regions.
- A customized landing zone that you build: You can also choose to build automation of AWS Landing Zone using custom automation tools and technologies. This approach will be using customer or partner managed orchestration and custom build components. Here, customer/partner is responsible for all the development, coding, integration and implementation. You will have to implement the baseline environment to get started with identity and access management, governance, data security, network design, and logging. You must also have enough expertise in AWS to manage, upgrade, maintain, and operate the solution once it’s deployed.
SIGNIFICANCE OF DRIFT WATCH
Monitor and control changes to stay compliant.
When a landing zone is created, it is compliant with the governance rules enforced by the chosen guardrails. As the landing zone is used by members of the organization, it may change the compliance status, creating a drift. These changes could be accidental or intentionally made to respond to some urgent operational requirements, but needs to be identified and resolved.
Drift Detection
Drift detection identifies resources that need changes or configuration updates to resolve the drift. AWS Control Tower automatically detects drifts and generates notifications in the audit trails. Member account administrators and master account administrators can receive such notifications and take necessary steps to resolve it.
Drift Resolution
Drift resolution needs to be done manually through the console or settings page. Some drifts can be repaired through settings page, others by can be resolved manually by administrators. If your landing zone is in a state of drift, the Enroll account feature in AWS Control Tower will not work. In such cases, you must provision new accounts through AWS Service Catalog. Examples of some of the Governance Drift are given below,
- Moved Member Account
- Added Member Account
- Removed Member Account
- Unplanned Update to Managed SCP
- SCP Attached to Member Account
- SCP Detached from Managed OU
- Deleted Managed OU
Resolving drift helps to ensure your compliance with governance regulations.
SUMMARY
AWS Landing Zone helps you start your cloud migration quickly and easily, following necessary best practices and security requirements out there in the industry. Recommend to choose and use the right automation tools for your AWS Landing Zone setup and management. Setting up is not enough, monitor, identify drifts and resolve it to be compliant always.
About The Author

Dr. Anil Kumar
VP Engineering
Founder | Architect | Consultant | Mentor | Advisor | Faculty
Solution Architect & IT Consultant with more than 25 yrs of IT Experience. Served in various roles, with both national and international institutions. Expertise in working with both legacy and advanced technology stacks and business domains.
